I have two questions for you.
- Is your vulnerability management process at its breaking point?
- Are you among the 68% of organizations that find it challenging to remediate critical vulnerabilities within 24 hours?
You should keep reading if you answered yes to either of these questions.
It’s no secret that the sheer volume of vulnerabilities your security teams must find, prioritize, and patch is overwhelming. With mounting risks and regulatory pressures, your security teams must navigate an increasingly complex web of threats. And the reality is, vulnerability management tools are at their breaking point—struggling to keep up with the speed and scale of today’s threats. And let’s be honest, legacy vulnerability management solutions aren’t cutting it.
At Swimlane, we understand your frustration of trying to stay ahead of endless vulnerability findings. That’s why we’re committed to delivering solutions that help you cut through the noise and take back control. Our mission is simple: to give you the clarity and AI automation needed to prioritize what matters most. With transparency at our core, we empower enterprises and MSSPs with the right tools to prevent breaches, ensure compliance, and finally break free from the chaos of vulnerability management.
But how are security teams handling critical vulnerability management challenges? To find out, we partnered with Sapio Research to survey 500 cybersecurity decision-makers across the U.S. and the U.K. In our latest report, Under Pressure: Is Vulnerability Management Keeping Up?
Throughout this blog series, we’ll break down key findings and explore how teams can overcome these obstacles with smarter, more efficient solutions.
Untangle the Vulnerability Management Chaos: A Web of Complexity
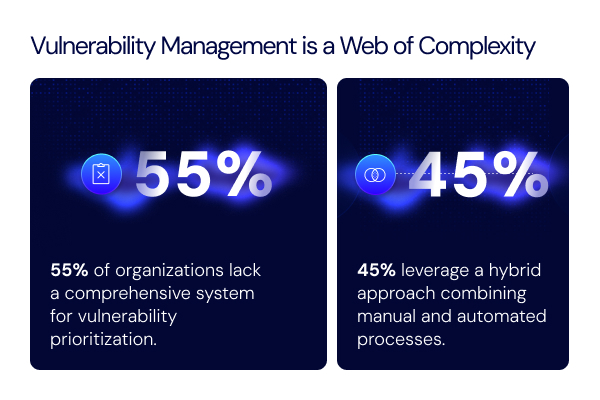
One of the most striking findings from our survey is that over half (55%) of organizations lack a comprehensive system for vulnerability prioritization. This gap means that vulnerabilities are often managed in a fragmented way, making it harder for teams to focus on the most critical threats. Vulnerability management processes are typically reactive (as are most solutions nowadays), relying on a hybrid approach that mixes manual efforts with automation — a solution that, while helpful, is far from optimal.However, the complexity doesn’t end there. It’s not uncommon for organizations to use multiple vulnerability scanning tools across their attack surface. For example:
- 71% of respondents use cloud security posture management
- 60% of respondents use multiple endpoint scanners
- 59% of respondents use web application scanners
While vulnerability scanners are a necessary starting point, the multiple-scanner reality leads to fragmented data and challenges prioritizing the findings that matter most. So I raise two key questions to you:
- How many vulnerability scanners does your team rely on?
- Do you struggle to prioritize and act on findings across different tools?
If you answered yes to either question, your vulnerability management process could be at its breaking point.
The Two Rat Races: Life & Vulnerabilities
You’re likely already in a rat race against life, work, and everything in between. But unfortunately, there’s another race you can’t afford to lose: the race against vulnerabilities. Because, let’s be honest, zero days aren’t uncommon anymore, and they wait for no one.
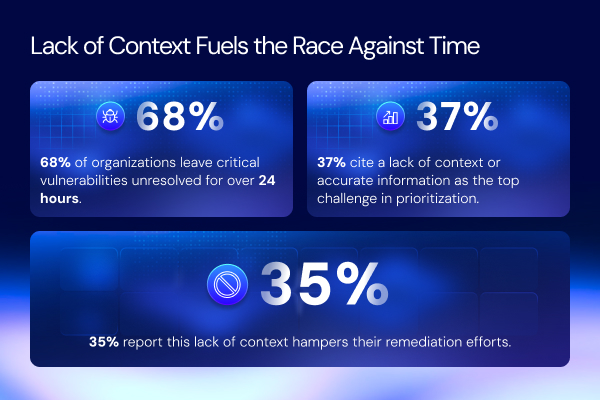
Speed is essential when remediating vulnerabilities, yet 68% of organizations report that it takes more than 24 hours to remediate a critical vulnerability. So, what’s holding teams back?
According to 37% of respondents, the biggest challenge in prioritizing and remediating vulnerabilities is the lack of context or accurate information. With over 39,000 new vulnerabilities identified in 2024 alone, survey respondents agree, they’re struggling to keep up with the volume sharing they often work with incomplete data, leading to delays and inefficiencies.
This lack of context contributes to slower response times and increases the chances of vulnerabilities slipping through the cracks. Given these growing threats, time is of the essence, and you need more intelligent solutions that enable faster, more informed decision-making.
The Hidden Costs of Manual Efforts They Don’t Warn You About
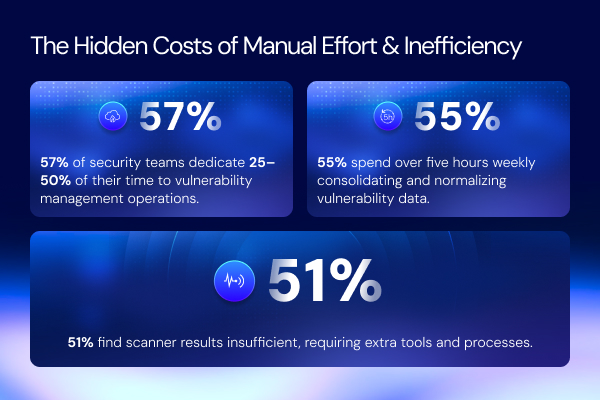
Here’s something you may already know, but let’s dive a bit deeper. According to respondents from the report, manual processes are draining security teams’ time and resources. Go figure, right? Check out these numbers from the report:
- More than half of survey respondents (57%) report that their teams spend 25% to 50% of their time on manual tasks related to vulnerability management operations.
This includes the time-consuming process of consolidating and normalizing vulnerability data, which 55% of organizations spend over five hours each week alone. Read that again. Five hours EACH week…
These inefficiencies are costly, with businesses losing an estimated $47,580 per employee annually due to the manual efforts involved in vulnerability management.
As attack surfaces expand and threats evolve at an unrelenting pace, the flaws in traditional vulnerability management tools are becoming impossible to ignore. Another question for you:
- Are you or your security team already stretched thin?
If you answered yes, without change and a more efficient approach, your entire system might buckle under pressure—pushing it to a breaking point.
Regulatory Compliance: The Necessary Evil
Regulatory compliance… It’s like doing your taxes. Very mundane, often overlooked, but essential to succeed or to be… well compliant! With that being said, the pressure to meet regulatory requirements is only growing, and the stakes are higher than ever.
- 65% of organizations express concerns that their vulnerability management programs may not satisfy a regulatory audit.
- 73% of respondents fear potential fines due to inadequate vulnerability management practices.
With more stringent regulations and increased scrutiny from regulatory bodies, your organization is facing heightened risks. As we’ll explore in future posts, effective vulnerability management is critical to avoiding costly penalties and reputational damage.

Tips to Turn Your Vulnerability Chaos into Clarity
It’s time to break free from the rat race against vulnerabilities, as the current state of vulnerability management is unsustainable. The respondents from the report make it clear: security teams are drowning in fragmented data, siloed processes, and time-consuming manual tasks. In other words, both security teams and their vulnerability management tools are at their breaking points. So, if you’re stuck in the same rat race as the survey respondents, it’s time for a smarter, more efficient approach. Here are five tips that will help turn your vulnerability chaos into clarity:
- Consolidate Vulnerability Data
Unify vulnerability data from multiple scanners for a comprehensive view and better decision-making. - Automate Prioritization and Remediation
Leverage automation to quickly prioritize vulnerabilities and speed up remediation efforts, reducing manual workload. - Facilitate Cross-Team Collaboration
Enable seamless workflows and communication between security, IT, and compliance teams to improve efficiency. - Use Context for Smarter Decisions
Incorporate threat intelligence and asset data to provide context for better vulnerability prioritization and response. - Ensure Continuous Monitoring and Adaptation
Implement real-time monitoring and adaptive processes to stay ahead of emerging threats and keep your vulnerability management strategy agile.
By embracing the Swimlane Vulnerability Response Management (VRM) solution you will achieve these five tips, streamline processes, and make data-driven decisions. You can finally take control of your vulnerability management chaos and focus on what truly matters most— your data, your job, your organization, YOU.

Swimlane Vulnerability Response Management Solution
The Swimlane Vulnerability Response Management (VRM) Solution closes the loop on Vulnerability Management. It is the industry’s most intelligent solution for smarter risk prioritization and management.
Check out this datasheet to learn how it can help you avoid breaches, compliance failures and costly penalties.