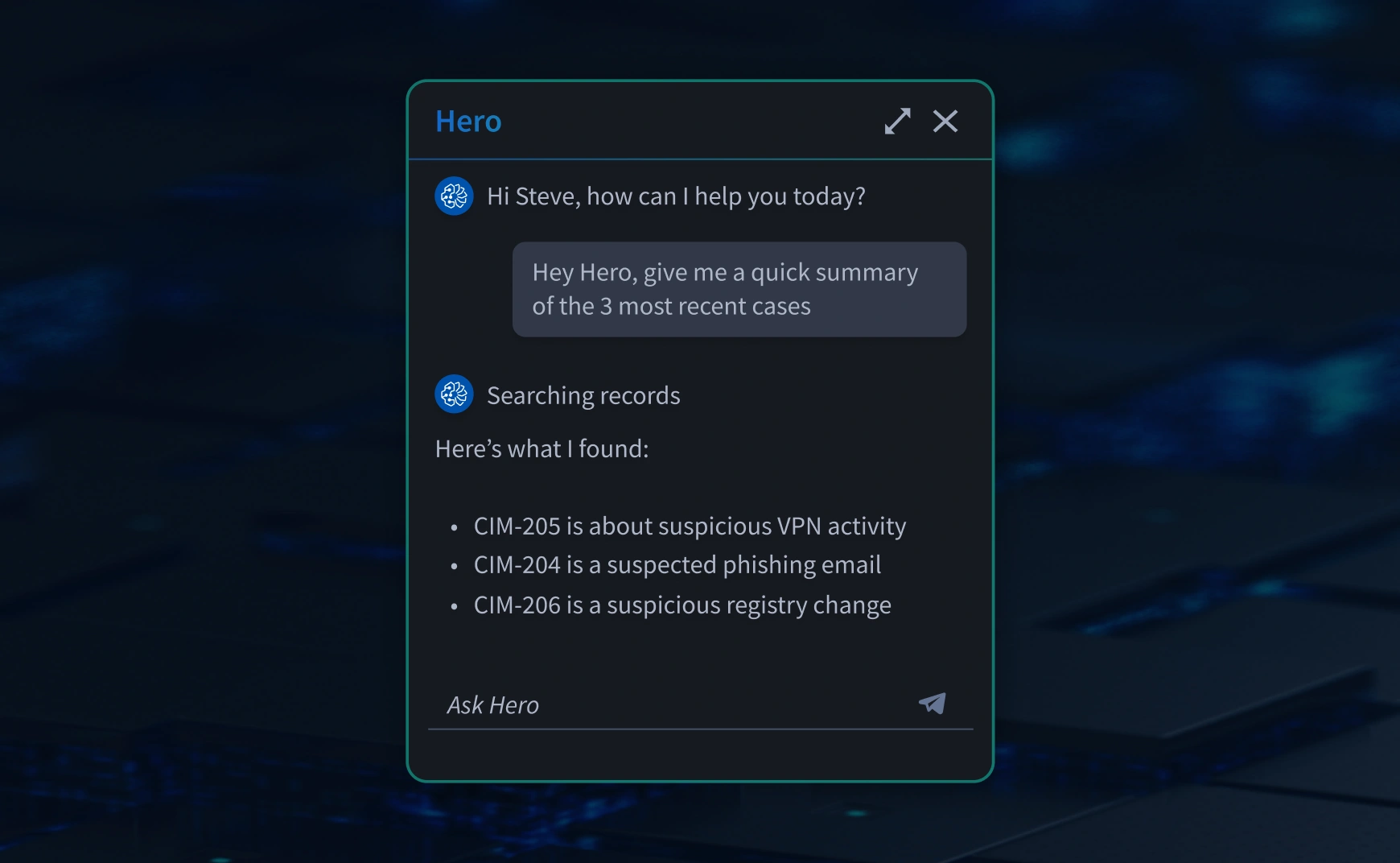
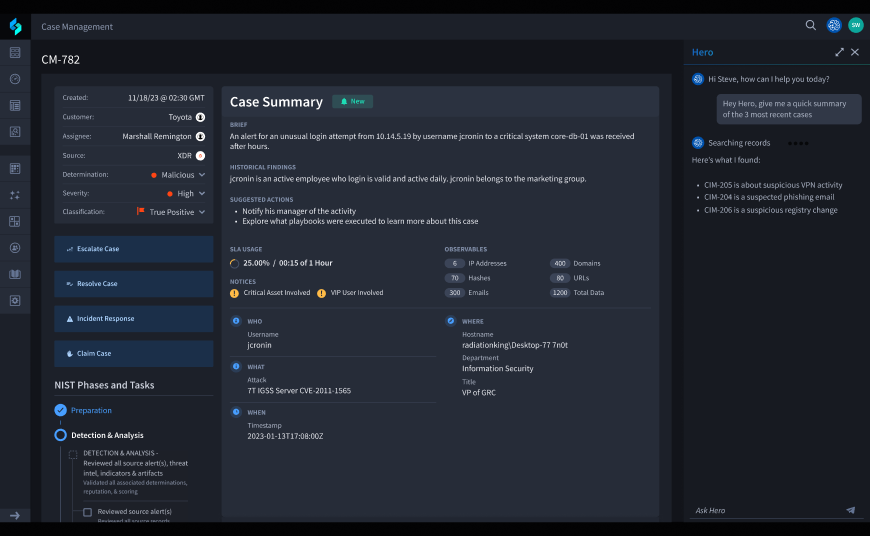
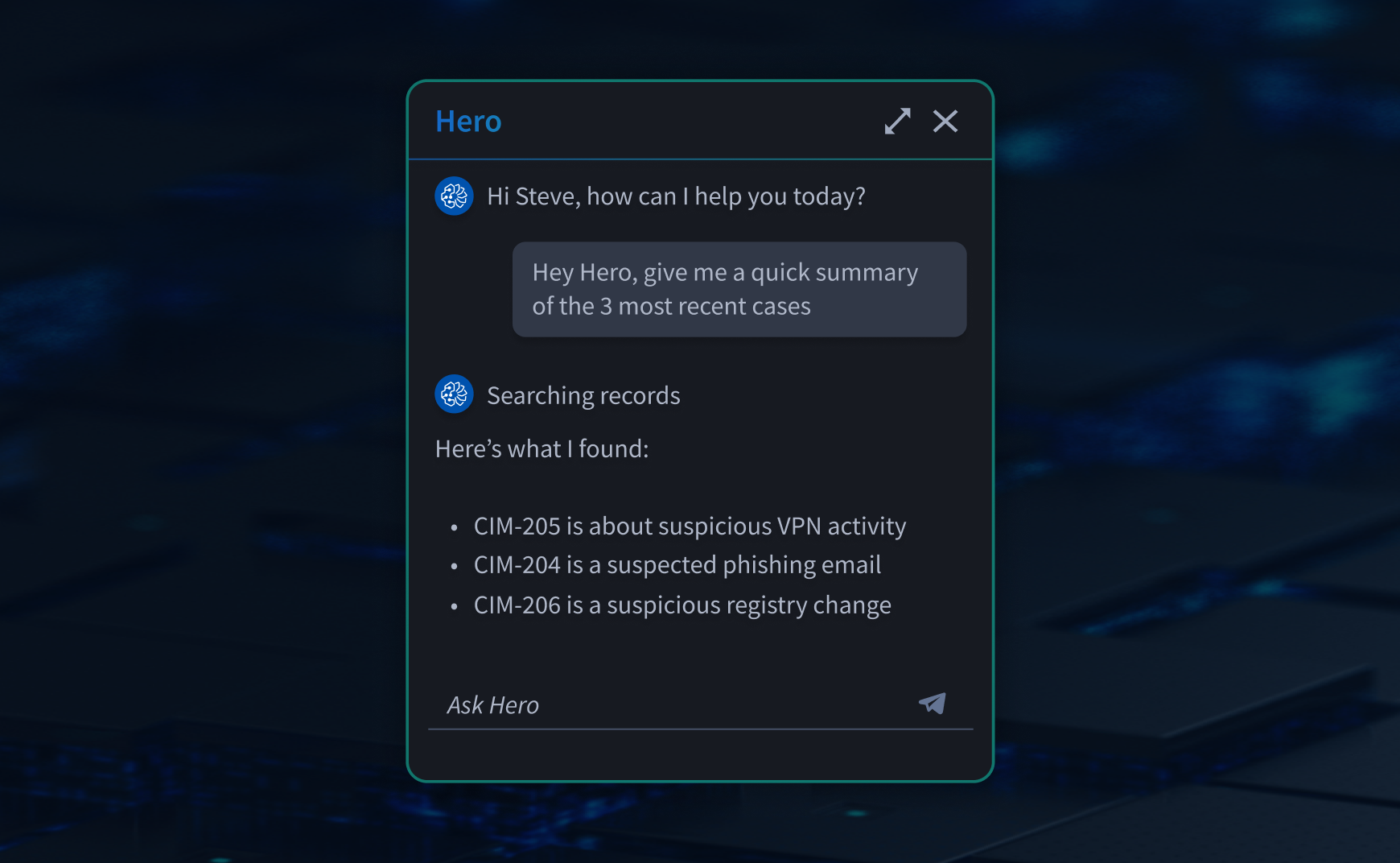
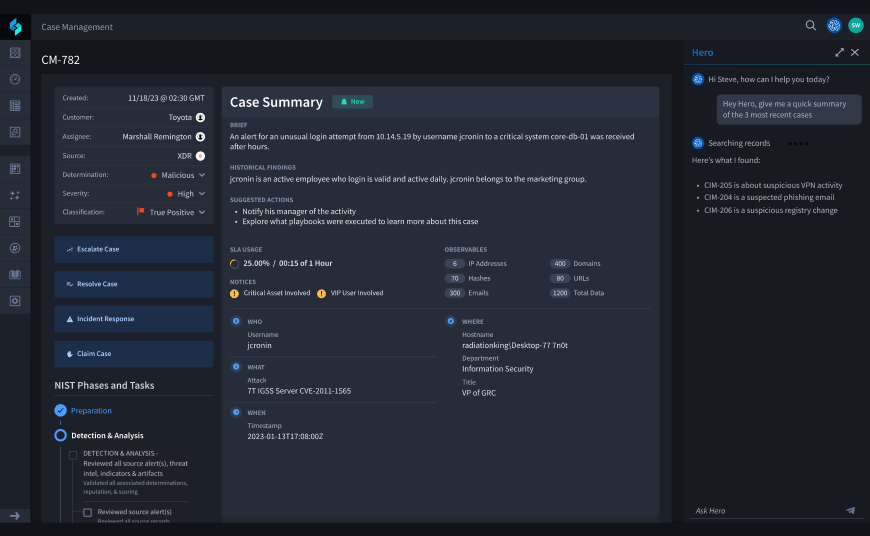
Hero AI powers instant execution
Empower your analyst team to execute automated responses using AI prompts to speed ad-hoc investigations and responses.
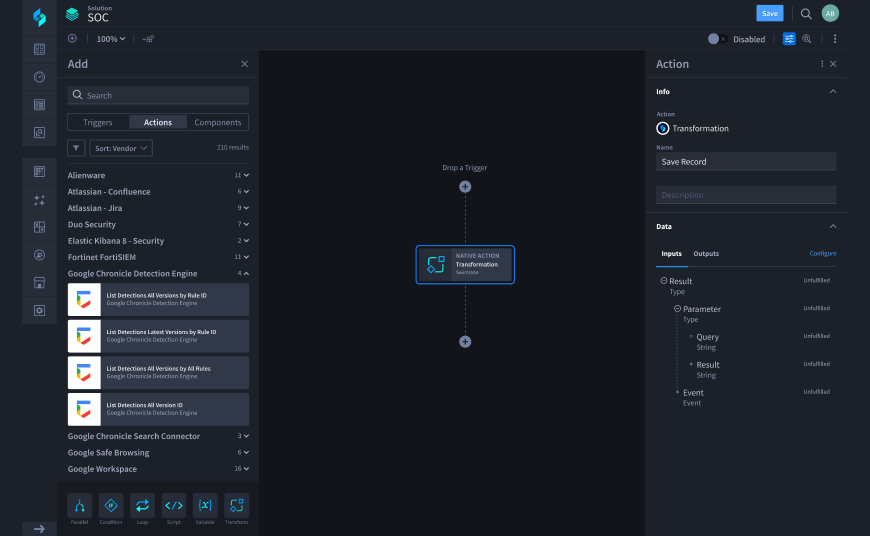
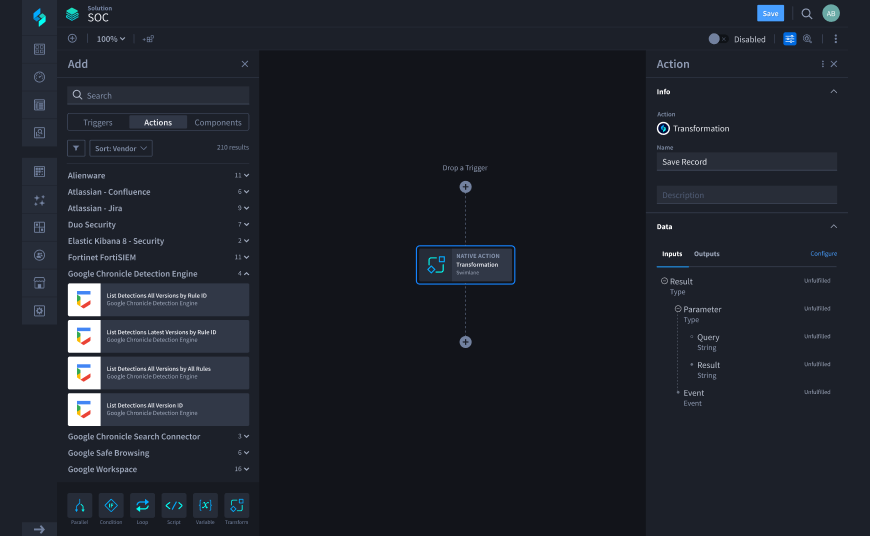
Generate or modify active playbooks at enterprise-scale
Instantly create enterprise-grade playbooks with the Hero AI Playbook Generator Agent, accelerating time-to-value and prototyping.
Deploy expert agents across your SOC
Scale SecOps by integrating expert AI agents into playbooks to manage dynamic reasoning with full context and guardrails.
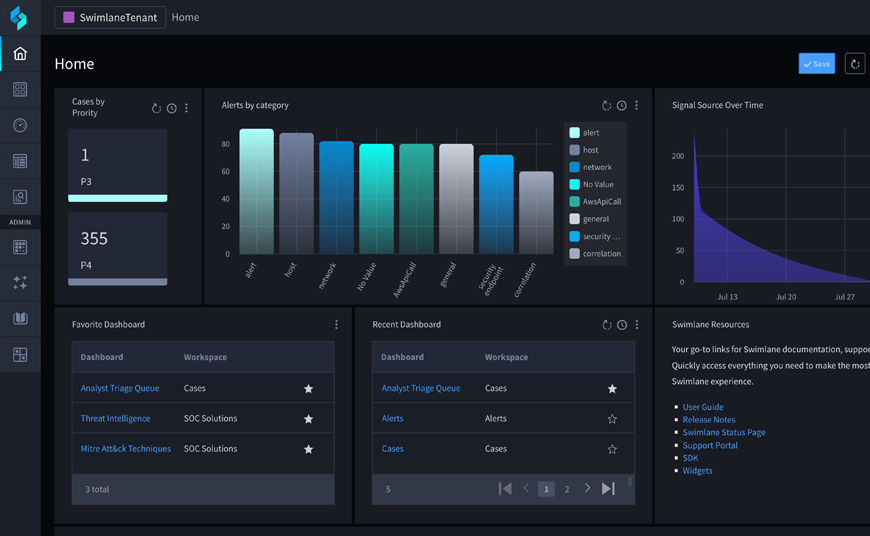
Hero AI powers instant and consistent service delivery
Prompt Hero AI to execute ad-hoc playbook actions across all customer environments to lighten analysts’ workload and deliver consistent decisions 24/7.
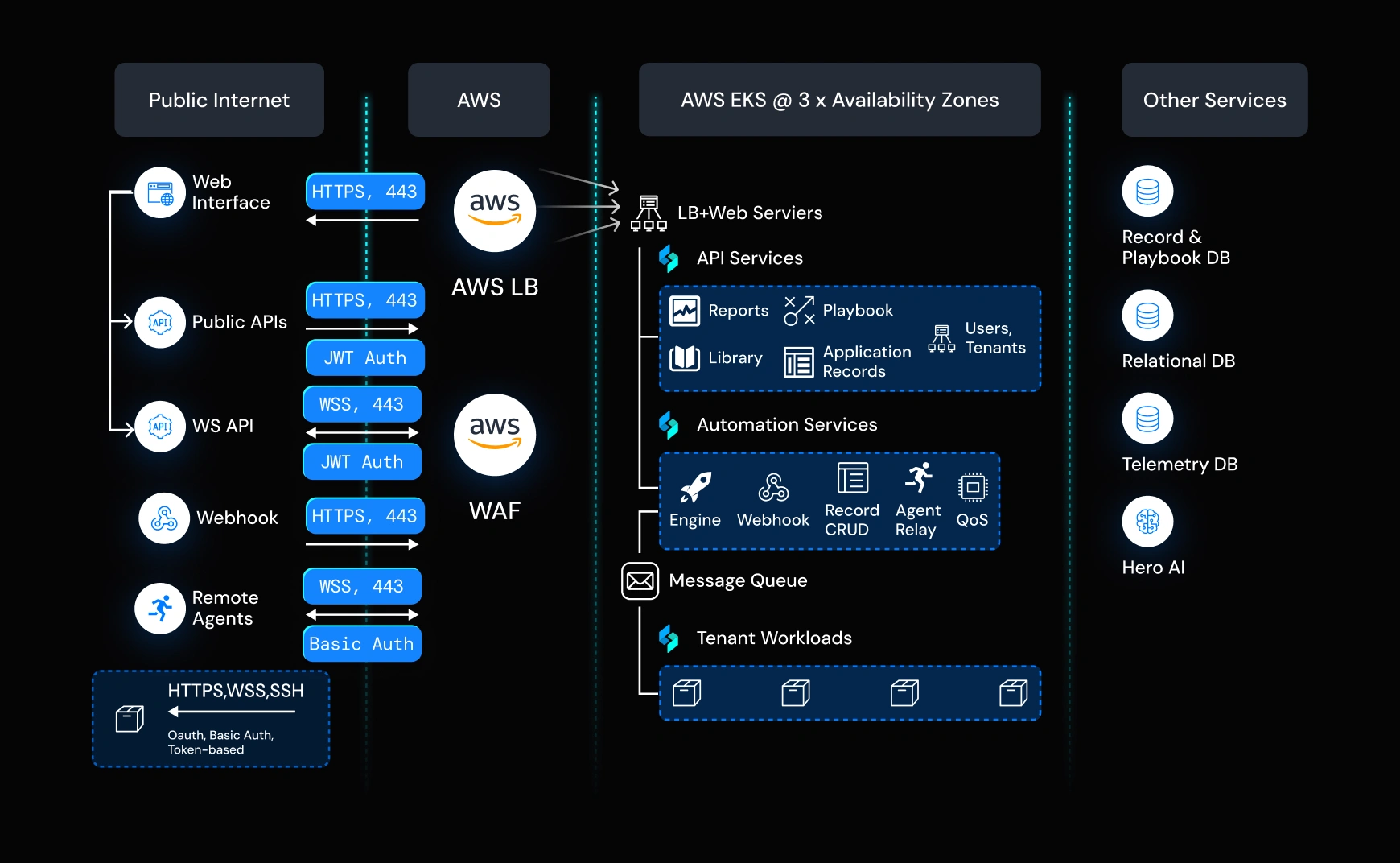
Generate and scale active playbooks across all tenants
Instantly create and deploy transparent production-grade playbooks with our Playbook Generator Agent, ensuring rapid time-to-service and accelerated value for every client.
Deploy expert agents to maximize analyst utilization
Leverage expert AI agents within the guardrails of deterministic playbooks for consistent investigative depth, transforming linear labor costs into scalable service delivery.
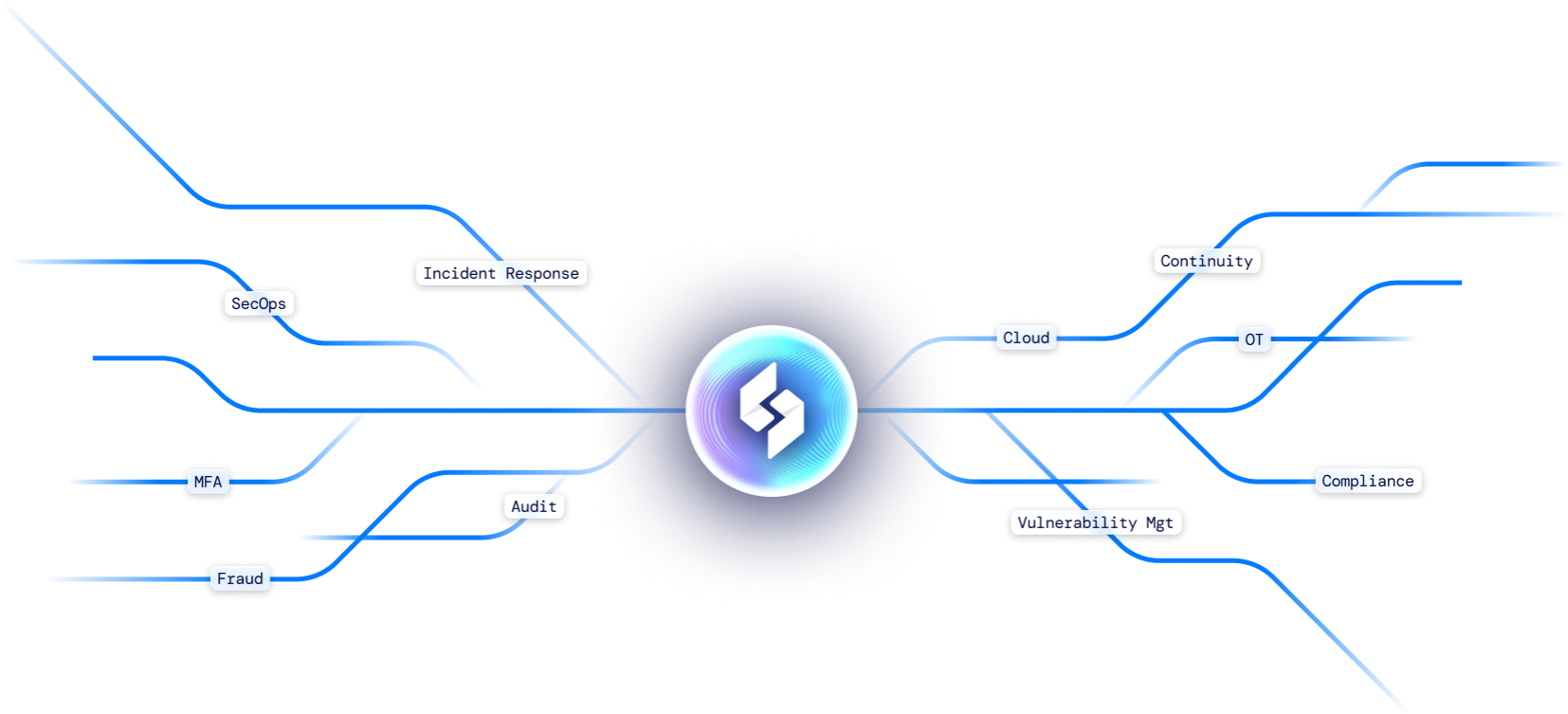
Agentic AI automation solutions for the work you hate
Is complexity holding you back?
SWIMLANE AI AGENTS
Power your security workforce with expert AI agents and our new agent-builder.
SWIMLANE AI AGENTS
Your business – now faster, AI-automated, and more profitable
Our Customers
Trusted by the World’s Leading Organizations

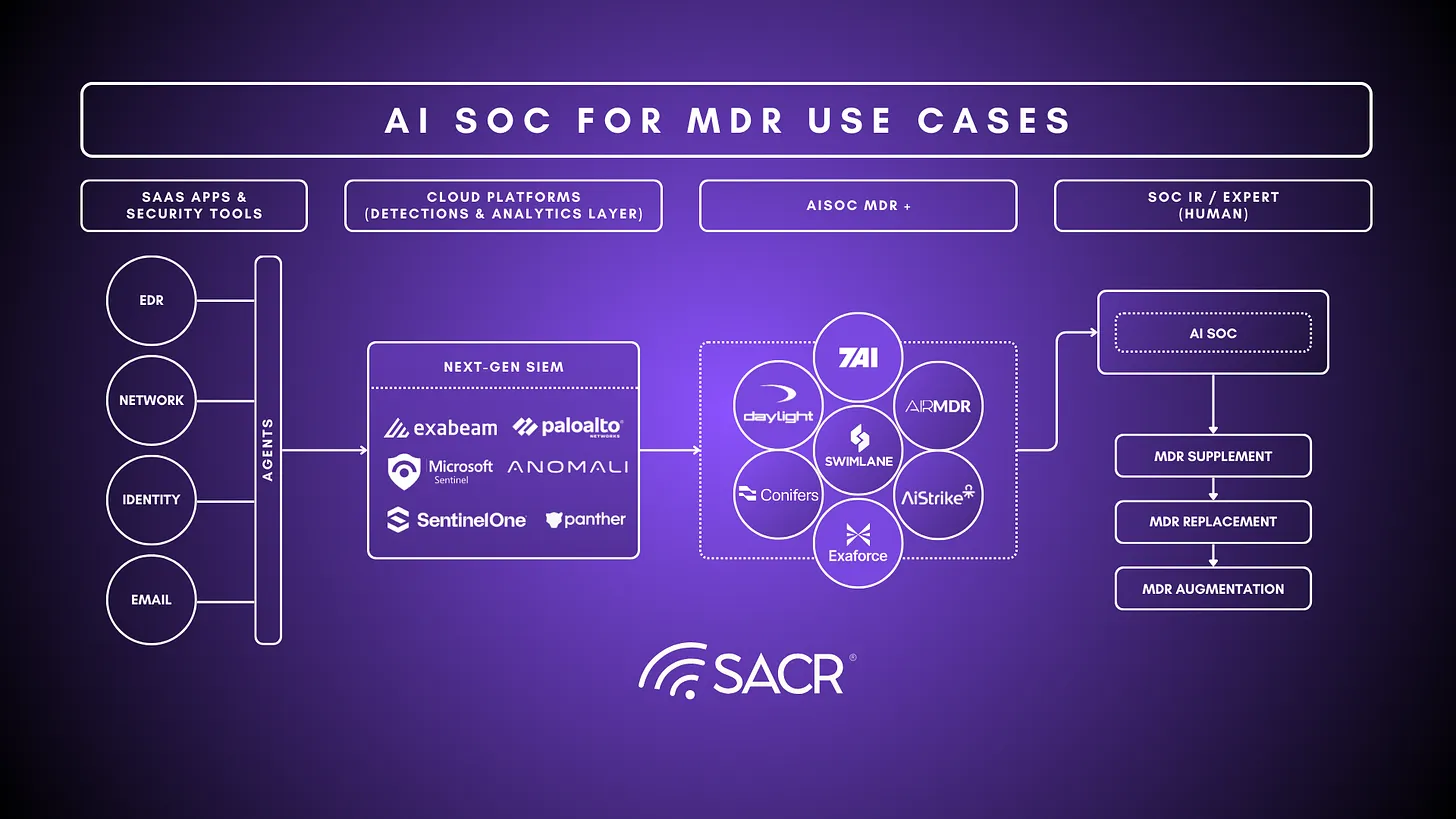
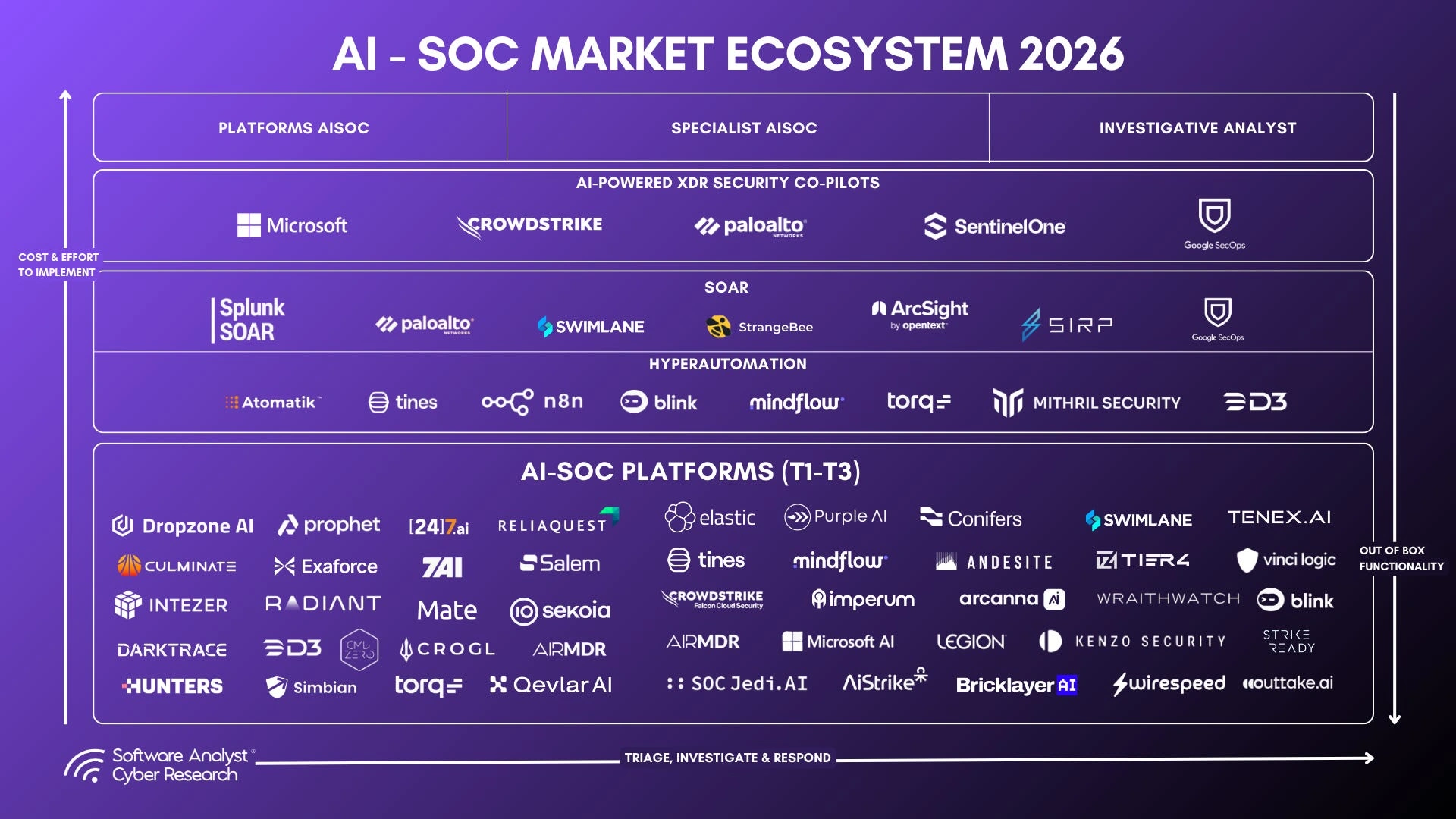
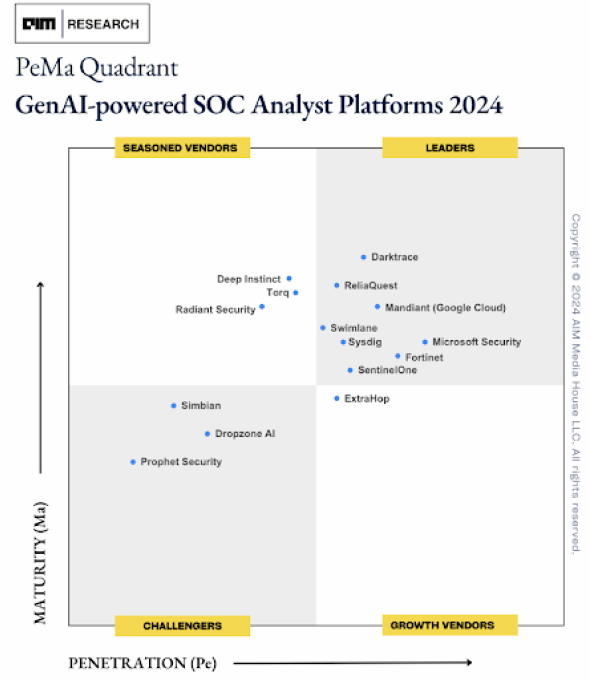
Get an AI SOC market overview from Software Analyst Cyber Research
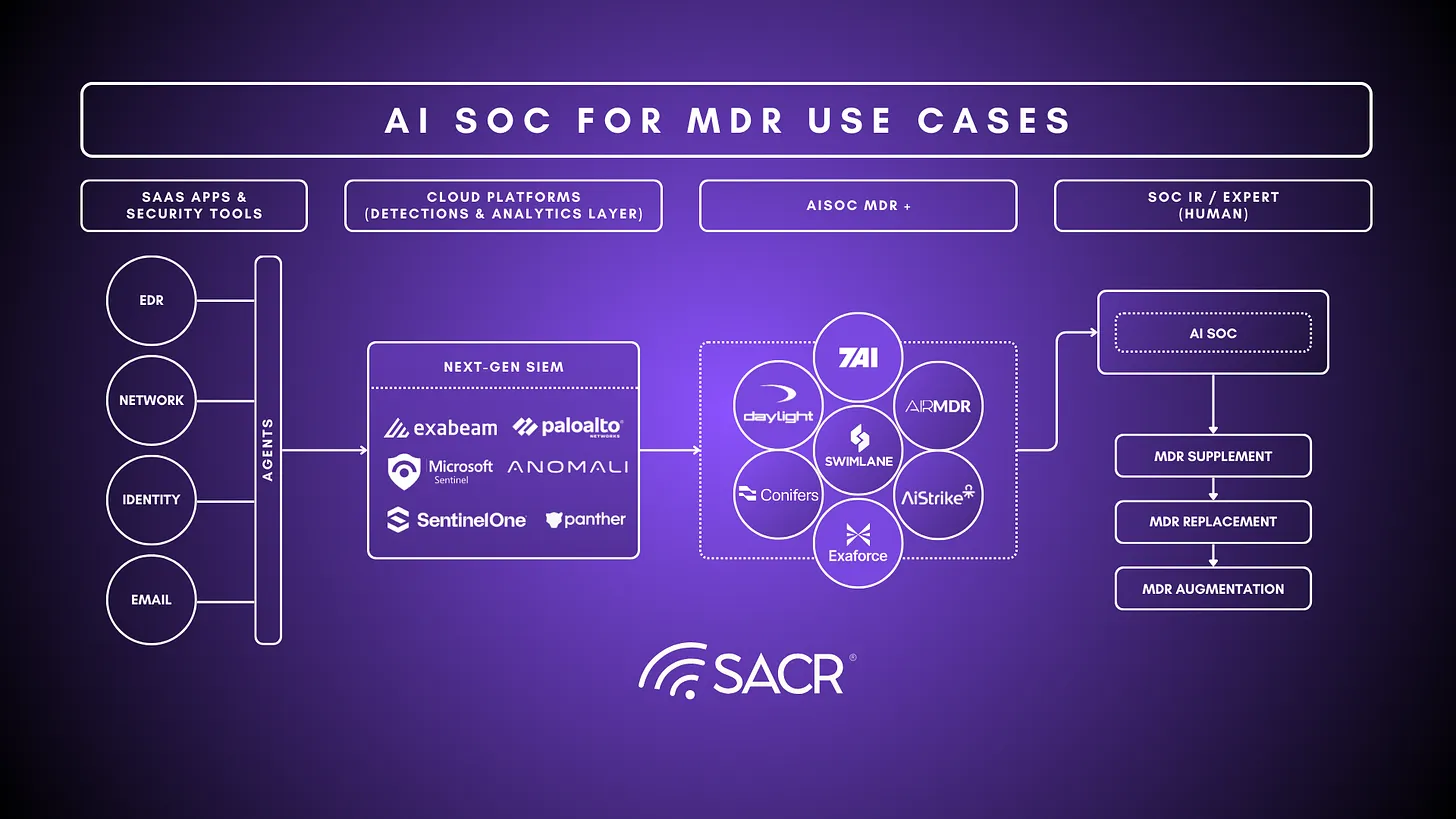
Get the AI SOC report for MDR