alerts per day
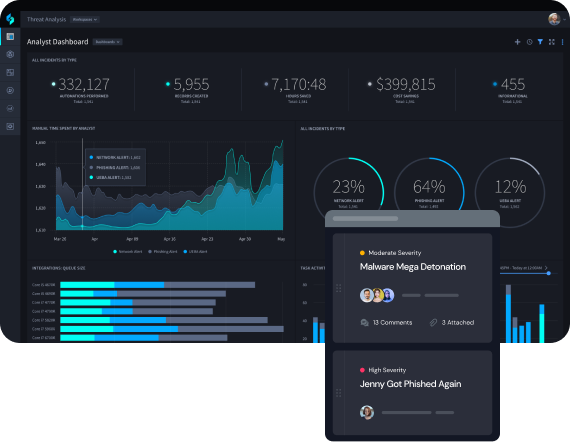
Security analysts working at large enterprises triage upwards of 10,000 alerts per day, with zero room for error.
Unfilled Security Jobs
Million
The global security workforce is expected to be 3.5 million workers short of globally available positions by 2025.
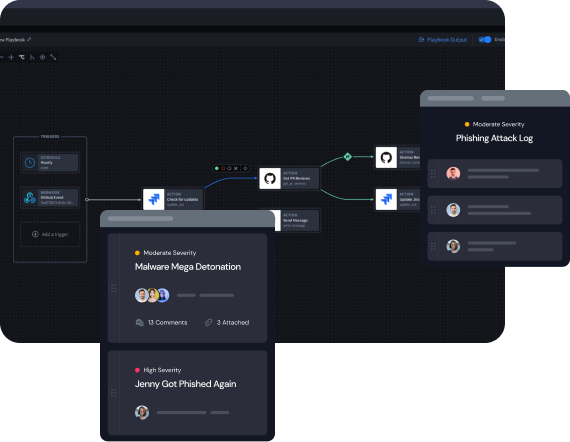
Why Low-Code Security Automation
Automation is a must-have for modern SOC teams to keep up with the growing threat landscape. But a lot has changed since the inception of SOAR over a decade ago. Low-code security automation offers a solution that hits the sweet spot of being powerful enough to automate anything but flexible enough for anyone to use.
FEATURES
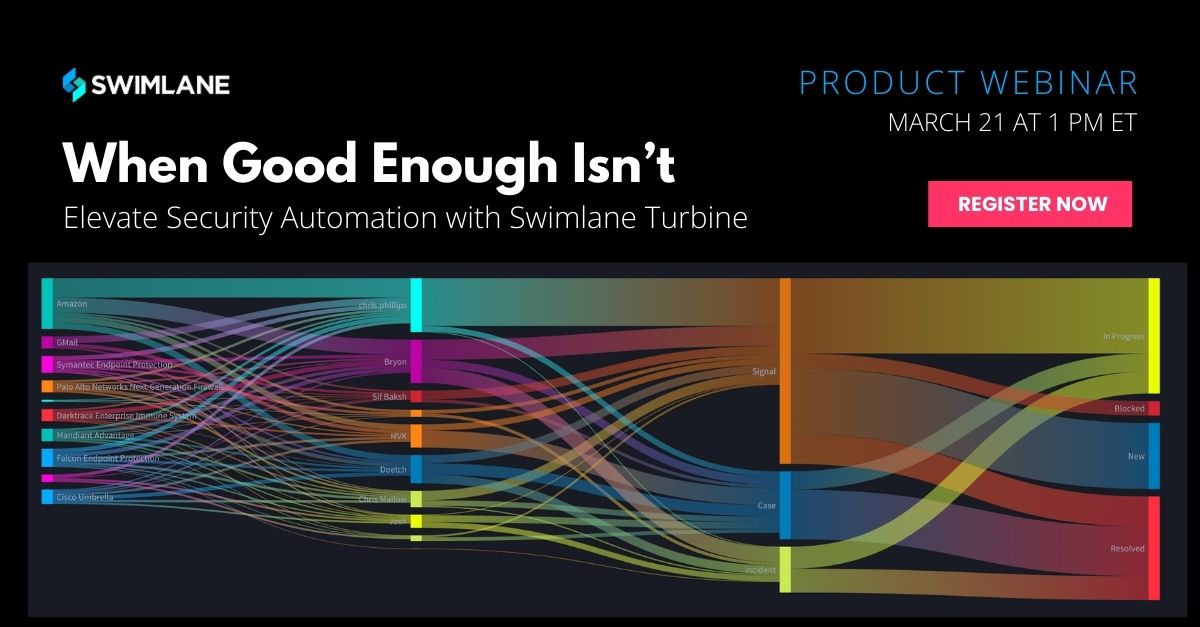
End-to-end Solutions for Any SecOps Process
Security Automation platforms provide solutions that make it easy to rapidly execute security best practices. Swimlane Turbine adapts to your organization’s unique security requirements and operational processes to automate tasks that typically require jumping between third-party systems.
FEATURES
Ready to Get Started?