An overview of Digital Forensics and Incident Response plans, and how to utilize automation for better response.
What is DFIR?
A Digital Forensics and Incident Response (DFIR) plan is a systematic and documented method of approaching and managing situations resulting from IT security incidents or breaches as well as collecting evidence related to the incident or data breach. DFIR plans are used in enterprise IT environments and facilities to identify, respond, limit and counteract security incidents as they occur.
Digital Forensics is the process of using scientific techniques and tools to identify, preserve and analyze system data in the event of a potential attack. It involves analyzing digital devices, such as computers, mobile devices and other endpoints to identify and extract evidence of “who” and “what” is involved with the incident.
Incident Response refers to the overall process that prepares for, identifies, responds to, and mitigates the effects of a security incident. It involves identifying the source of the incident, determining the extent of the damage, and taking steps to prevent further harm.
The Value of DFIR
The best way to handle an incident is by being prepared and having already taken the necessary proactive steps. This involves a specific process of:
- Identify a set of individuals to make up the incident response team
- Make sure they are well-trained for any procedures they may need to execute
- Create a detailed document called the incident response plan
- Regularly practice and update the incident response plan
The DFIR plan should have detailed steps for each type of incident that identifies the actions to be carried out, the order in which they should be executed, and which team members are involved. It is not a question of if you need to have a process and plan for digital forensics and incident response. It is only a matter of when you will be using it.
DFIR Plan Overview
Traditional digital forensics and incident response is dependent on physical systems and physical access. However, most organizations now run one or more of their services in the cloud. To address modern hybrid infrastructures your digital forensics and incident response plan must account for systems that are virtual and located outside your premises.
What Are the Steps of the DFIR Process?
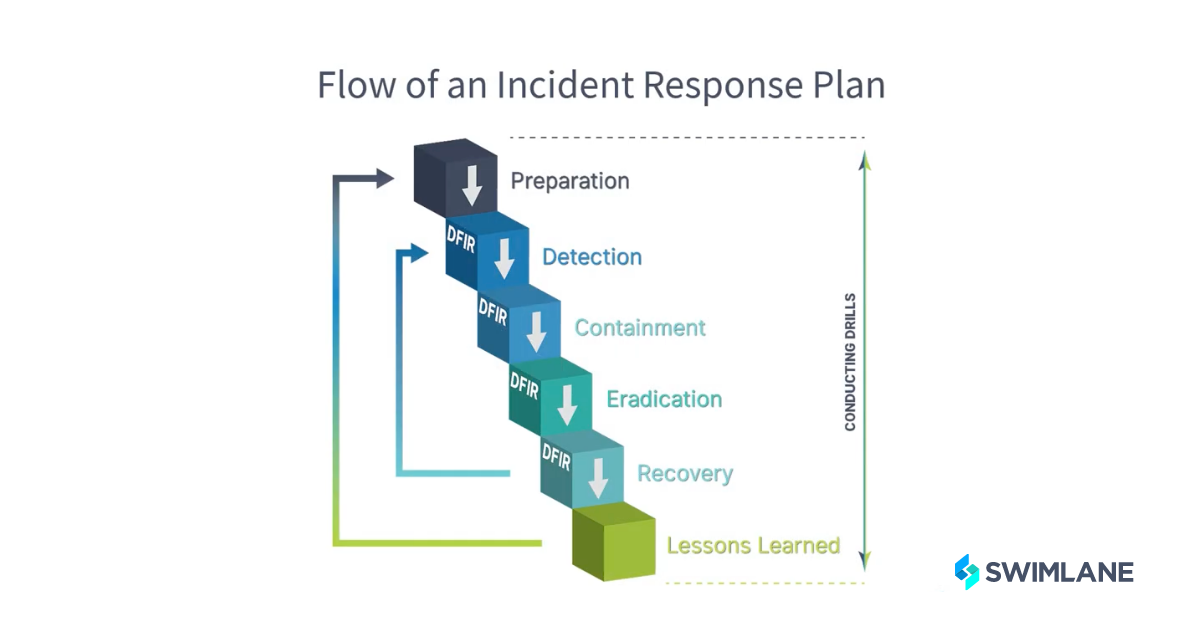
The following list offers videos that examine each phase of the DFIR plan and the important differences when implementing your plan with cloud resources:
Preparation: Preparation ensures that the DFIR is ready to execute when needed. Preparation also ensures that personnel is trained and that infrastructure and software needs are met ahead of time.
Detection: Detection handles the initial identification and triage of an incident and establishes a chain of command for the incident response through investigation and documentation. A low-code security orchestration, automation and response (SOAR) platform can automate the ingestion of alerts or events from any number of security and networking devices on your network, as well as monitor email inboxes.
Containment: Containment stops the incident from increasing in severity or scope. Containment protects the organization. A SOAR platform can orchestrate various security and networking tools to gather evidence from a system, shut off network access to a system, power down systems, and correlate alerts and incidents to help identify spreading compromises.
Eradication: Eradication eliminates the root cause of an incident to secure affected assets and prevent further breaches. A low-code SOAR platform can automate collecting backup data from a system, reimagining a system, redeploying containers and running on-system malware scans or scripts.
Recovery: Recovery restores pre-incident functionality to affected systems. A SOAR platform can use scripts or vendor tools to push standard images to systems, restore backed-up data to assist in the recovery process, as well as verify whether expected access and behavior have been restored.
Post-Incident Activity: A “lessons learned” exercise is a retrospective focused on improving processes & procedures. An incident report based on the timeline of the incident is created and agreed on. The report should identify when things happened and ensure everyone agrees with the details. The lessons learned phase is often overlooked or skipped but it is very important because it reviews the incident and finds opportunities for improvements in the incident response plan and the overall security posture.
Watch our in-depth video series on the DFIR Process.
Benefits of Automating the DFIR Process
Automating digital forensics and incident response processes can provide useful benefits, such as:
- Better consistency and precision of actions
- Increase in speed and accuracy
- Better tracking of what is taking place
- Reduced divergence from the plan itself
The process of gathering all data related to a case from multiple tools, environments, and sources can be automated with a low-code security automation platform. Most SOAR solutions allow data to be exported or reported in various formats.

Calculate your ROI with Swimlane Turbine
To help companies evaluate the potential financial impact of the potential investment, TAG Cyber conducted an extensive study on the Swimlane Security Automation Solution.


